
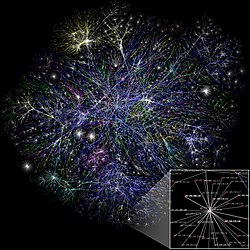
In network science, the Configuration Model is a family of random graph models designed to generate networks from a given degree sequence. Unlike simpler models such as the Erdős–Rényi model, Configuration Models preserve the degree of each vertex as a pre-defined property. This flexibility allows the modeler to construct networks with arbitrary degree distributions, making it widely used as a reference model for real-life networks, particularly in social, biological, and technological domains. The concept of "Configuration Model" was first introduced by Béla Bollobás, who laid the foundation for its application in graph theory and network science.
| Part of a series on | ||||
| Network science | ||||
|---|---|---|---|---|
| ||||
| Network types | ||||
| Graphs | ||||
|
||||
| Models | ||||
|
||||
| ||||
Rationale for the model
The key advantage of the Configuration Model lies in its ability to decouple the degree sequence from specific edge generation processes. This makes it suitable for analyzing networks with heterogeneous degree distributions, such as scale-free networks, which exhibit heavy-tailed degree distributions. By preserving these structural properties, Configuration Models provide a null hypothesis for understanding the role of degree distributions in shaping network properties.
Configuration Models can be specified for different types of graphs:
- Simple graphs: Graphs without self-loops or multi-edges.
- Multi-edge graphs: Graphs allowing multiple edges between the same pair of nodes.
- Loopy graphs: Graphs that include self-loops (edges connecting a node to itself).
- Directed graphs: Models with specified in-degrees and out-degrees for each node.
- Undirected graphs: Models that consider the total degree of each node.
Configuration Models
The family of Configuration Models can be categorized into two main groups:
- Microcanonical Configuration Models: Fix the degree sequence exactly.
- Canonical Configuration Models: Fix the degree sequence in expectation.
Micro-Canonical Configuration Model
The Micro-Canonical Configuration Model is the most common variation of the configuration model. It exactly preserves the degree sequence of a given graph by assigning stubs (half-edges) to nodes based on their degrees and then randomly pairing the stubs to form edges.
The preservation of the degree sequence is exact in the sense that all realizations of the model result in graphs with the same predefined degree distribution. This variation is referred to as micro-canonical because it defines a uniform probability space where all possible graphs consistent with the given degree sequence are equally likely to be sampled. This approach ensures that the degree sequence is strictly maintained.
The model can be formalized as stub-labelled model, where stubs are explicitly labelled and paired; alternatively, it can be formalised as a vertex-labelled models, where edges between vertices are indistinguishable.
Canonical Configuration Models
Canonical Configuration Models relax the exact degree sequence constraint and preserve it only in expectation. These models define probability distributions over the edges of the network. Canonical configuration models are often referred to as soft configuration models.
Chung-Lu Configuration Model
The Chung-Lu Configuration Model is a canonical configuration model variant for simple graphs (i.e., without multi-edges). It assumes that edges between nodes are independent from each other, differently from the micro-canonical model. The probability of an edge between nodes and is proportional to the product of their degrees and, in the case of a loopy undirected graph, is given by:
where and are the degrees of nodes and , and is the total number of edges in the graph. In this formulation, the expected degree sequence matches the input degrees, but the actual degree sequence in any realization may vary slightly due to the probabilistic nature of edge formation.
Application: Modularity Calculation
The Chung-Lu configuration model, provides the benchmark in the calculation of network modularity. Modularity measures how well a network is divided into modules or communities, comparing the observed structure against a null model: the configuration model. The modularity is computed as:
where:
- is the adjacency matrix of the observed network, with if there is an edge between and , and otherwise.
- represents the expected probability of an edge between nodes and under the configuration model.
- is the Kronecker delta, equal to 1 if nodes and are in the same module and 0 otherwise.
This equation compares the observed network to the configuration model, where edges are distributed based solely on the degree sequence. Modularity scores provide insights into the quality of community structures in the network, with higher scores indicating stronger modularity.
For further details, refer to the page on modularity.
Norros-Reittu Configuration Model
The Norros-Reittu Configuration Model extends the Chung-Lu configuration model by allowing for multi-edges between nodes. In this model, the number of edges between nodes and follows a Poisson distribution, given by:
where is the expected number of edges between nodes and , defined as: Here: and are the degrees of nodes and , respectively. is the total number of edges in the graph. As for Chung-Lu configuration model, nodes pairs are assumed to be independent from each other.
Connection to Degree-Corrected Stochastic Block Model:
The Norros-Reittu Configuration Model is particularly important as it provides the degree correction for the Degree-Corrected Stochastic Block Model (DC-SBM). By incorporating the degree sequence into the edge probability, this model allows the DC-SBM to distinguish between structural patterns in communities and variations driven by node degrees. This degree correction ensures that the observed degree heterogeneity in networks does not bias the identification of community structures.
Casiraghi-Nanumyan Hypergeometric Configuration Model
The Casiraghi-Nanumyan Hypergeometric Configuration Model extends canonical configuration models by accounting for dependencies between edges. Unlike models assuming independent edge generation, this model uses a multivariate hypergeometric distribution to represent the probability of an entire graph configuration. This approach preserves the degree sequence while modeling competition for resources. The probability of observing a specific graph with adjacency matrix is given by:
where is the number of edges between nodes and , represents the propensity for interaction between nodes and based on their degrees, is the total number of edges in the graph and .
This model captures resource competition by enforcing that the sum of interactions across all node pairs is fixed. Forming an edge between two nodes reduces the availability of resources for other connections, reflecting realistic constraints in systems like social or ecological networks. The model naturally generates multi-edges for any node pair and where .
Configuration Model from Maximum Entropy Principles
Starting from the maximum entropy principle, one can generate another canonical configuration model, referred to as the soft configuration model. This model belongs to the family of exponential random graph models (ERGMs) and generates random graphs by constraining the expected degree sequence while maximizing the entropy of the graph model. The probability of a graph is given by:
where are Lagrange multipliers ensuring the expected degree of node matches the target degree, is the degree of node in the graph .
Generating from the Micro-Canonical Configuration Model
The following algorithm describes the generation of the model:
- Take a degree sequence, i. e. assign a degree to each vertex. The degrees of the vertices are represented as half-links or stubs. The sum of stubs must be even in order to be able to construct a graph (). The degree sequence can be drawn from a theoretical distribution or it can represent a real network (determined from the adjacency matrix of the network).
- Choose two stubs uniformly at random and connect them to form an edge. Choose another pair from the remaining stubs and connect them. Continue until you run out of stubs. The result is a network with the pre-defined degree sequence. The realization of the network changes with the order in which the stubs are chosen, they might include cycles (b), self-loops (c) or multi-links (d) (Figure 1).
Self-loops, multi-edges and implications
The algorithm described above matches any stubs with the same probability. The uniform distribution of the matching is an essential property in calculating other features of the generated networks. The network generation process does not exclude the development of a self-loop or a multi-link. If we designed the process where self-loops and multi-edges are not allowed, the matching of the stubs would not follow a uniform distribution.
The expected total number of multi-links in a configuration model network would be:
where is the n-th moment of the degree distribution. Therefore, the average number of self-loops and multi-links is a constant for some large networks, and the density of self-loops and multi-links, meaning the number per node, goes to zero as as long as is constant and finite. For some power-law degree distributions where the second moment diverges, density of multi-links may not vanish or may do so more slowly than .
A further consequence of self-loops and multi-edges is that not all possible networks are generated with the same probability. In general, all possible realizations can be generated by permuting the stubs of all vertices in every possible way. The number of permutation of the stubs of node is , so the number of realizations of a degree sequence is . This would mean that each realization occurs with the same probability. However, self-loops and multi-edges can change the number of realizations, since permuting self-edges can result an unchanged realization. Given that the number of self-loops and multi-links vanishes as , the variation in probabilities of different realization will be small but present.
Properties
Edge probability
A stub of node can be connected to other stubs (there are stubs altogether, and we have to exclude the one we are currently observing). The vertex has stubs to which node can be connected with the same probability (because of the uniform distribution). The probability of a stub of node being connected to one of these stubs is . Since node has stubs, the probability of being connected to is ( for sufficiently large ). Note that this formula can only be viewed as a probability if , and more precisely it describes the expected number of edges between nodes and . Note that this formula does not apply to the case of self-edges.
Given a configuration model with a degree distribution , the probability of a randomly chosen node having degree is . But if we took one of the vertices to which we can arrive following one of edges of i, the probability of having degree k is . (The probability of reaching a node with degree k is , and there are such nodes.) This fraction depends on as opposed to the degree of the typical node with . Thus, a neighbor of a typical node is expected to have higher degree than the typical node itself. This feature of the configuration model describes well the phenomenon of "my friends having more friends than I do".
Clustering coefficient
The clustering coefficient (the average probability that the neighbors of a node are connected) is computed approximately as follows:
where denotes the probability that a random edge reaches a degree- vertex, and the factors of the form "" rather than "" appear because one stub has been accounted for by the fact that these are neighbors of a common vertex. Evaluating the above results in
Using and , with denoting the degree distribution, denoting the average degree, and denoting the number of vertices, the above becomes
with denoting the second moment of the degree distribution. Assuming that and are constant, the above behaves as
where the constant depends on . Thus, the clustering coefficient becomes small in the limit.
Giant component
In the configuration model, a giant component (GC) exists if
where and are the first and second moments of the degree distribution. That means that, the critical threshold solely depends on quantities which are uniquely determined by the degree distribution .
Configuration model generates locally tree-like networks, meaning that any local neighborhood in such a network takes the form of a tree. More precisely, if you start at any node in the network and form the set of all nodes at distance or less from that starting node, the set will, with probability tending to 1 as n → ∞, take the form of a tree. In tree-like structures, the number of second neighbors averaged over the whole network, , is:
Then, in general, the average number at distance can be written as:
Which implies that if the ratio of is larger than one, then the network can have a giant component. This is famous as the Molloy-Reed criterion. The intuition behind this criterion is that if the giant component (GC) exists, then the average degree of a randomly chosen vertex in a connected component should be at least 2. Molloy-Reed criterion can also be expressed as: which implies that, although the size of the GC may depend on and , the number of nodes of degree 0 and 2 have no contribution in the existence of the giant component.
Diameter
Configuration model can assume any degree distribution and shows the small-world effect, since to leading order the diameter of the configuration model is just .
Components of finite size
As total number of vertices tends to infinity, the probability to find two giant components is vanishing. This means that in the sparse regime, the model consist of one giant component (if any) and multiple connected components of finite size. The sizes of the connected components are characterized by their size distribution - the probability that a randomly sampled vertex belongs to a connected component of size There is a correspondence between the degree distribution and the size distribution When total number of vertices tends to infinity, , the following relation takes place:
where and denotes the -fold convolution power. Moreover, explicit asymptotes for are known when and is close to zero. The analytical expressions for these asymptotes depend on finiteness of the moments of the degree distribution tail exponent (when features a heavy tail), and the sign of Molloy–Reed criterion. The following table summarises these relationships (the constants are provided in).
| Moments of | Tail of | ||
|---|---|---|---|
| light tail | -1 or 1 | ||
| 0 | |||
| heavy tail, | -1 | ||
| 0 | |||
| 1 | |||
|
|
heavy tail, | -1 | |
| 0 | |||
| 1 | |||
| heavy tail, | -1 | ||
| 0 | |||
| 1 | |||
|
|
heavy tail, | 1 | |
| heavy tail, | 1 |
Modelling
Comparison to real-world networks
Three general properties of complex networks are heterogeneous degree distribution, short average path length and high clustering. Having the opportunity to define any arbitrary degree sequence, the first condition can be satisfied by design. Still, as shown above, the global clustering coefficient is an inverse function of the network size, so for large configuration networks, clustering tends to be small. This feature of the baseline model contradicts the known properties of empirical networks, but extensions of the model can solve this issue. (see ). All the networks generated by this model are locally tree-like provided the average of the excess degree distribution is either constant or grows slower than the square root of number of links, . In other words, this model prevents forming substructures such as loops in the large size limit. Vanishing of clustering coefficient, is a special case of this more general result. While the tree-like property makes the model not very realistic, so many calculations, such as the generating function methods, are possible for the configuration model thanks to this feature.
Directed configuration model
In the DCM (directed configuration model), each node is given a number of half-edges called tails and heads. Then tails and heads are matched uniformly at random to form directed edges. The size of the giant component, the typical distance, and the diameter of DCM have been studied mathematically. There also has been extensive research on random walks on DCM. Some real-world complex networks have been modelled by DCM, such as neural networks, finance and social networks.

References
- ^ Network Science by Albert-László Barabási.
- Bollobás, B. (1980). A probabilistic proof of an asymptotic formula for the number of labelled regular graphs. European Journal of Combinatorics, 1(4), 311-316.
- ^ Newman, Mark (2010-03-25). Networks: An Introduction – Oxford Scholarship. Oxford University Press. doi:10.1093/acprof:oso/9780199206650.001.0001. ISBN 9780191594175.
- Fosdick, Bailey K., et al. "Configuring random graph models with fixed degree sequences." Siam Review 60.2 (2018): 315-355.
- Chung, Fan; Lu, Linyuan (2002-12-10). "The average distances in random graphs with given expected degrees". Proceedings of the National Academy of Sciences. 99 (25): 15879–15882. Bibcode:2002PNAS...9915879C. doi:10.1073/pnas.252631999. ISSN 0027-8424. PMC 138532. PMID 12466502.
- Newman, M. E. J. (2004). "Finding and evaluating community structure in networks". Physical Review E. 69 (2): 026113. arXiv:cond-mat/0308217. Bibcode:2004PhRvE..69b6113N. doi:10.1103/physreve.69.026113. PMID 14995526. S2CID 197314.
- Norros, I., & Reittu, H. (2006). On a conditionally Poissonian graph process. Advances in Applied Probability, 38(1), 59-75.
- Karrer, Brian, and Mark EJ Newman. "Stochastic blockmodels and community structure in networks." Physical Review E—Statistical, Nonlinear, and Soft Matter Physics 83.1 (2011): 016107.
- Casiraghi, Giona, and Vahan Nanumyan. "Configuration models as an urn problem." Scientific reports 11.1 (2021): 13416.
- ^ Newman, Mark (2018-10-18). Networks. Vol. 1. Oxford University Press. doi:10.1093/oso/9780198805090.001.0001. ISBN 978-0-19-880509-0.
- Molloy, Michael; Reed, Bruce (1995-03-01). "A critical point for random graphs with a given degree sequence". Random Structures & Algorithms. 6 (2–3): 161–180. CiteSeerX 10.1.1.24.6195. doi:10.1002/rsa.3240060204. ISSN 1098-2418.
- Chung, Fan; Lu, Linyuan (2002-12-10). "The average distances in random graphs with given expected degrees". Proceedings of the National Academy of Sciences. 99 (25): 15879–15882. Bibcode:2002PNAS...9915879C. doi:10.1073/pnas.252631999. ISSN 0027-8424. PMC 138532. PMID 12466502.
- ^ Kryven, I (2017). "General expression for the component size distribution in infinite configuration networks". Physical Review E. 95 (5): 052303. arXiv:1703.05413. Bibcode:2017PhRvE..95e2303K. doi:10.1103/PhysRevE.95.052303. hdl:11245.1/fa1b270b-61a5-4f20-b496-ddf446fdfe80. PMID 28618550. S2CID 8421307.
- Barabási, Albert-László; Albert, Réka (1999-10-15). "Emergence of Scaling in Random Networks". Science. 286 (5439): 509–512. arXiv:cond-mat/9910332. Bibcode:1999Sci...286..509B. doi:10.1126/science.286.5439.509. ISSN 0036-8075. PMID 10521342. S2CID 524106.
- Watts, Duncan J.; Strogatz, Steven H. (1998). "Collective dynamics of 'small-world' networks". Nature. 393 (6684): 440–442. Bibcode:1998Natur.393..440W. doi:10.1038/30918. ISSN 1476-4687. PMID 9623998. S2CID 4429113.
- "Configuration Models and Complex Networks". danlarremore.com. Retrieved 2024-11-28.
- Newman, M. E. J. (2009). "Random Graphs with Clustering". Physical Review Letters. 103 (5): 058701. arXiv:0903.4009. Bibcode:2009PhRvL.103e8701N. doi:10.1103/physrevlett.103.058701. PMID 19792540. S2CID 28214709.
- ^ COOPER, COLIN; FRIEZE, ALAN (May 2004). "The Size of the Largest Strongly Connected Component of a Random Digraph with a Given Degree Sequence". Combinatorics, Probability and Computing. 13 (3): 319–337. doi:10.1017/S096354830400611X. ISSN 1469-2163. S2CID 27511938.
- Cai, Xing Shi; Perarnau, Guillem (10 April 2020). "The giant component of the directed configuration model revisited". arXiv:2004.04998 .
- van der Hoorn, Pim; Olvera-Cravioto, Mariana (June 2018). "Typical distances in the directed configuration model". The Annals of Applied Probability. 28 (3): 1739–1792. arXiv:1511.04553. doi:10.1214/17-AAP1342. S2CID 13683470.
- Cai, Xing Shi; Perarnau, Guillem (10 March 2020). "The diameter of the directed configuration model". arXiv:2003.04965 .
- Bordenave, Charles; Caputo, Pietro; Salez, Justin (1 April 2018). "Random walk on sparse random digraphs". Probability Theory and Related Fields. 170 (3): 933–960. arXiv:1508.06600. doi:10.1007/s00440-017-0796-7. ISSN 1432-2064. S2CID 55211047.
- Caputo, Pietro; Quattropani, Matteo (1 December 2020). "Stationary distribution and cover time of sparse directed configuration models". Probability Theory and Related Fields. 178 (3): 1011–1066. doi:10.1007/s00440-020-00995-6. hdl:11385/196435. ISSN 1432-2064. S2CID 202565916.
- Cai, Xing Shi; Perarnau, Guillem (14 October 2020). "Minimum stationary values of sparse random directed graphs". arXiv:2010.07246 .
- Amini, Hamed (1 November 2010). "Bootstrap Percolation in Living Neural Networks". Journal of Statistical Physics. 141 (3): 459–475. arXiv:0910.0627. Bibcode:2010JSP...141..459A. doi:10.1007/s10955-010-0056-z. ISSN 1572-9613. S2CID 7601022.
- Amini, Hamed; Minca, Andreea (2013). "Mathematical Modeling of Systemic Risk". Advances in Network Analysis and its Applications. Mathematics in Industry. Vol. 18. Springer. pp. 3–26. doi:10.1007/978-3-642-30904-5_1. ISBN 978-3-642-30903-8. S2CID 166867930.
- Li, Hui (July 2018). "Attack Vulnerability of Online Social Networks". 2018 37th Chinese Control Conference (CCC). pp. 1051–1056. doi:10.23919/ChiCC.2018.8482277. ISBN 978-988-15639-5-8. S2CID 52933445.
 and
and  is proportional to the product of their degrees and, in the case of a loopy undirected graph, is given by:
is proportional to the product of their degrees and, in the case of a loopy undirected graph, is given by:

 and
and  are the degrees of nodes
are the degrees of nodes  is the total number of edges in the graph. In this formulation, the expected degree sequence matches the input degrees, but the actual degree sequence in any realization may vary slightly due to the probabilistic nature of edge formation.
is the total number of edges in the graph. In this formulation, the expected degree sequence matches the input degrees, but the actual degree sequence in any realization may vary slightly due to the probabilistic nature of edge formation.

 is the
is the  if there is an edge between
if there is an edge between  otherwise.
otherwise. represents the expected probability of an edge between nodes
represents the expected probability of an edge between nodes  is the Kronecker delta, equal to 1 if nodes
is the Kronecker delta, equal to 1 if nodes 
 is the expected number of edges between nodes
is the expected number of edges between nodes  Here:
Here:
 is given by:
is given by:

 represents the propensity for interaction between nodes
represents the propensity for interaction between nodes  .
.
 .
.
 is given by:
is given by:

 are
are  is the degree of node
is the degree of node  ). The degree sequence can be drawn from a theoretical distribution or it can represent a real network (determined from the
). The degree sequence can be drawn from a theoretical distribution or it can represent a real network (determined from the  stubs and connect them. Continue until you run out of stubs. The result is a network with the pre-defined degree sequence. The realization of the network changes with the order in which the stubs are chosen, they might include cycles (b), self-loops (c) or multi-links (d) (Figure 1).
stubs and connect them. Continue until you run out of stubs. The result is a network with the pre-defined degree sequence. The realization of the network changes with the order in which the stubs are chosen, they might include cycles (b), self-loops (c) or multi-links (d) (Figure 1).
 is the n-th
is the n-th  as long as
as long as  is constant and finite. For some power-law degree distributions where the second moment diverges, density of multi-links may not vanish or may do so more slowly than
is constant and finite. For some power-law degree distributions where the second moment diverges, density of multi-links may not vanish or may do so more slowly than  .
.
 , so the number of realizations of a degree sequence is
, so the number of realizations of a degree sequence is  . This would mean that each realization occurs with the same probability. However, self-loops and multi-edges can change the number of realizations, since permuting self-edges can result an unchanged realization. Given that the number of self-loops and multi-links vanishes as
. This would mean that each realization occurs with the same probability. However, self-loops and multi-edges can change the number of realizations, since permuting self-edges can result an unchanged realization. Given that the number of self-loops and multi-links vanishes as  other stubs (there are
other stubs (there are  stubs altogether, and we have to exclude the one we are currently observing). The vertex
stubs altogether, and we have to exclude the one we are currently observing). The vertex  . Since node
. Since node  (
( for sufficiently large
for sufficiently large  , and more precisely it describes the expected number of edges between nodes
, and more precisely it describes the expected number of edges between nodes  , the probability of a randomly chosen node
, the probability of a randomly chosen node  is
is  . (The probability of reaching a node with degree k is
. (The probability of reaching a node with degree k is  , and there are
, and there are  such nodes.) This fraction depends on
such nodes.) This fraction depends on  as opposed to the degree of the typical node with
as opposed to the degree of the typical node with  (the average probability that the neighbors of a node are connected) is computed approximately as follows:
(the average probability that the neighbors of a node are connected) is computed approximately as follows:

 denotes the probability that a random edge reaches a degree-
denotes the probability that a random edge reaches a degree- " rather than "
" rather than "
 and
and  , with
, with  denoting the average degree, and
denoting the average degree, and  denoting the number of vertices, the above becomes
denoting the number of vertices, the above becomes

 denoting the second moment of the degree distribution. Assuming that
denoting the second moment of the degree distribution. Assuming that 
 limit.
limit.

 or less from that starting node, the set will, with probability tending to 1 as n → ∞, take the form of a tree. In tree-like structures, the number of second neighbors averaged over the whole network,
or less from that starting node, the set will, with probability tending to 1 as n → ∞, take the form of a tree. In tree-like structures, the number of second neighbors averaged over the whole network,  , is:
, is: 

 is larger than one, then the network can have a giant component. This is famous as the Molloy-Reed criterion. The intuition behind this criterion is that if the giant component (GC) exists, then the average degree of a randomly chosen vertex
is larger than one, then the network can have a giant component. This is famous as the Molloy-Reed criterion. The intuition behind this criterion is that if the giant component (GC) exists, then the average degree of a randomly chosen vertex  which implies that, although the size of the GC may depend on
which implies that, although the size of the GC may depend on  and
and  , the number of nodes of degree 0 and 2 have no contribution in the existence of the giant component.
, the number of nodes of degree 0 and 2 have no contribution in the existence of the giant component.
 .
.
 - the probability that a randomly sampled vertex belongs to a connected component of size
- the probability that a randomly sampled vertex belongs to a connected component of size  There is a correspondence between the degree distribution
There is a correspondence between the degree distribution  When total number of vertices tends to infinity,
When total number of vertices tends to infinity, 
 and
and  denotes the
denotes the  -fold
-fold  and
and  is close to zero. The analytical expressions for these asymptotes depend on finiteness of the moments of
is close to zero. The analytical expressions for these asymptotes depend on finiteness of the moments of  the degree distribution tail exponent
the degree distribution tail exponent  (when
(when 




















 . In other words, this model prevents forming substructures such as loops in the large size limit. Vanishing of clustering coefficient, is a special case of this more general result. While the tree-like property makes the model not very realistic, so many calculations, such as the
. In other words, this model prevents forming substructures such as loops in the large size limit. Vanishing of clustering coefficient, is a special case of this more general result. While the tree-like property makes the model not very realistic, so many calculations, such as the